Email How To
Business Email SecurityEmail How To – Business Email Security [updated 8-17-20]

Email How To
Building a professional business but then sending your communications from a free email provider, e.g. yahoo.com, aol.com or gmail.com screams "amateur" and worse, it puts your email at risk. These free email providers are favorite targets for spammers, hackers and malware.
One of the first things you can do to increase your security and promote a more professional image, is to take charge of your communications, especially email. The following steps will go a long way towards that goal.
Note: We'll be using DNS - Domain Naming System - to configure and secure our business email. Think of DNS as a sort of online phone book. It stores the online addresses, including your website address and your email address so that when someone wants to visit your website or send you an email, DNS provides the "directions" to reach you and/or your business.
Where you manage your DNS records may vary depending on whether you've chosen to use your domain name registrar, e.g. Goaddy, Namecheap, etc., your web hosting provider or a third party, e.g. Cloudflare, to manage your DNS. If you're not sure, then your first order of business is to gather this critical information. Read this post 5 Cypersecurity Tips for Small Business, to learn what information you should must document. For our example below, we'll be using the Cloudflare dashboard to manage our DNS.
5 6 Steps to set up and secure your business email.
Step 1: Create your MX record
Important; separate your email server from your webserver.
Why? If spammers infiltrate your email, your email server ip address could get blacklisted.
This could prevent you from sending emails until your ip is removed from the blacklist.
BUT even worse, it could also result in problems for your webserver because they are using the same ip that is blacklisted!
If your webserver is hosted on it's own unique ip, it will be unaffected should your email server's ip get blacklisted.
There are two ways to do this:
- Good: Use a unique ip address for your email server which is different than the ip address of your webserver. You can get a unique dedicated ip for as little as $1/month so there's really no reason not to. Just tell your web host you want a dedicated ip for email only and a different one for your webserver.
- Better: Host your email on a different server than your webserver. This could be another server dedicated to only email or a third party ESP (email service provider). This will prevent attacks against your email server from having any effect on your webserver.
Also, if you're using a proxy server to add a layer of protection for your webserver by hiding the webserver's ip address, having your email server and webserver use the same ip will expose your ip address because the email MX record (see below) must be public.
Thus your cover is blown and hackers can now target your ip with a denial of service (DoS) attack!
Using a unique ip for your email server will mitigate the blacklisting possibilities but if both ips are still on the same server (option 1) a denial of service attack against one ip can still negatively affect the entire server's resources.
Hence, option 2 is best if at all possible.
Now that you have a dedicated ip for your email server, you'll want to configure a DNS record to tell email senders where your email server is located.
This component is called the MX record - mail exchange record. This record tells the email sender how to locate your email server.
It's required in order to allow your domain to receive email and it looks like the following (yourdomain.com would be replaced with your actual domain name):

This MX record points to another type of DNS record called an A record.
The A record points to the ip address of your mail server.
Note that in the above example, the host name mail could also be labeled email or whatever name your want to designate for your mail server, as long as there is a corresponding A record for that host.
Now that you have your email up and running, we need to add some additional DNS records to better protect your email from hackers and spammers.
I'll be using the Cloudflare DNS dashboard for our examples. Cloudflare is a DNS registrar and also provides security and performance for businesses of all size. Your DNS management interface may appear different, depending on where you're managing your DNS, e.g. Godaddy, Namecheap, etc. The basics remain the same though, regardless of the management interface.
Step 2: Create a DNS record of type SPF (sender policy framework).
This will be a TXT type of record and will look like this:

In the above example, the "v" stands for version, in this case this is version 1 (spf1).
Next is the ip address of your mail server that is allowed to send mail for your domain.
Note that you can specify more than one server, as shown above.
The modifier ~all means that all mail servers are listed here but if mail comes from a different server, the host should accept the mail but mark it as spf failure. To reject all mail from any other servers than the ones listed, change ~ to -, example: -all.
Creating a proper spf record will help to deter spammers.
Step 3: Create a DKIM (DomainKeys Identified Mail) record
In your cPanel dashboard, in the email group, click the option Email Deliverability.
You will now see a message noting if your DKIM is installed and
the option "Manage". Clicking Manage will allow you to view your DKIM configuration.
If you are using a third party, e.g. Cloudflare to manage your DNS, you can simply click Copy to copy and paste the contents when creating your DKIM record at Cloudflare.

Create a DNS record of type TXT. In the NAME field, default is called the selector and is assigned by your mail server (or sending server if using a third party like sendgrid.com, google.com, etc.
In our example, the "v" stands for version, so in our example this version 1 of your DKIM record.
The domain keys are encrypted using a cryptographic algorithm called "rsa".
Finally, p= is your actual public key which is a long encrypted, complex string of characters and numbers.

Once you have configured and published your DKM record, you can perform a free DKIM lookup to validate your DKIM record.
Step 4: Create a DMARC policy
source: sendgrid
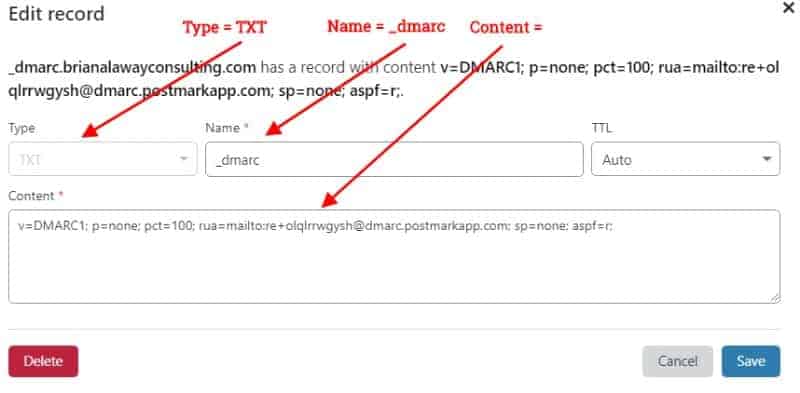
To create your DMARC policy, we will need to add a DNS record of TYPE TXT. For the name, we'll use _dmarc. In the Content area, we'll need to add our DMARC values. The v= stands for version, pct is the percentage of our emails that will be subject to our DMARC policy, rua is the mail to url that reports will be sent to, sp is the action that we want our policy to take (none will only report policy failures and reject will reject emails which fail our DMARC policy. It's highly recommended that initially you should configure your DMARC policy with the "none" parameter which will enable reporting only. This will allow you to identify any false positives or correct any miss-configurations. Once you're satisfied with your DMARC results, switch the parameter from "none" to "reject", minus the quotes.
Putting it all together, our DMARC policy will check for spf and dkim failures and execute our designated DMARC policy.
Step 5: Email Encryption
In order to prevent someone from intercepting and viewing your emails, you'll need to make sure that whatever email client you are using is configured to send secure (encrypted) emails over secure ports. Check your client software documentation for instructions on configuring your email client to use specific ports.
Receiving emails
There are two protocols for receiving emails:
POP3 which uses port 995 for receiving secure inbound mail.
IMAP which uses port 993 for receiving secure inbound mail.
The major difference is that by default, POP3 will download your mail for local storage and remove it from the server. Individual apps, e.g. Outlook, may allow you to control how long messages will be available on your server before being removed.
IMAP will, by default, leave messages on your server to allow for simultaneous access from different devices, e.g. laptop, tablet or phone.
Sending emails
SMTP is the protocol used for sending:
Port 587 is currently the recommended port for sending secure mail.
In the past, port 465 was also used for secure outbound mail. It's still in use today so check with your email service provider to verify which ports are available. Most of the major email vendors now recommend port 587 for encrypted email.

BONUS: Add a PTR record to help prevent your emails from getting blocked or being flagged as spam. The PTR (a.k.a. Pointer record) record maps an ip address back to a host name. This is just the reverse of the A record function, which is to map a host name to an ip address. Consequently, the PTR record is referred to as a reverse lookup.
For example, when a receiving server receives an email from a sending server claiming to be mail.example.com, it can perform a reverse lookup for mail.example.com. If the ip address listed in the PTR record matches that of the sending server, the receiving server will accept the mail.
Some receiving servers may accept the mail even if the host names do not match but the ips of those domains match. For example, mail.domain1.com sends an email and the receiving server performs a reverse lookup and sees the listing in the PTR record pointing to mail.domain2.com. The receiving server then performs a forward lookup for mail.domain2.com and the ip matches that for mail.domain1.com so the receiving server accepts the mail even though the host names are different.
NOTE: If you use Cloudflare, the PTR record type option listed in the record type dropdown is NOT a PTR record for reverse lookup for mail. Instead it is a PTR record for forward lookup of the domain.
via Cloudflare
"The main reason to have a PTR record is to prevent emails from ending up in spam folders. Since Cloudflare doesn't support email traffic by default, you would instead need to set the PTR record where your email server is located."
Ask you web host or email hosting provider to create your PTR record.
Step 6: Filter emails by country
If you use cPanel email, you can use the available country filter in WHM. To block a country, log into WHM and in the search, type exim.
Choose Exim Configuration Manager from the results. Then in the search box on the right, type country. Now click Manage to access the allowed/blocked countries list.

Click the box to Select All, then click Block Selected to block ALL countries. The Allowed toggle should turn grey (off).

Now from the list, select the countries you want to Allow incoming email and click the green Allow Selected button. The on/off toggle should turn blue.

Understand that this filters email based on the ip of the sending server. Thus it's possible that someone from a blocked country could still get their email through if the sending server is located in an allowed country. Never the less, this filter could still prove effective for blocking many unwanted emails.
In conclusion
Follow the steps above and you'll not only promote your brand in a more professional manner with your own branded emails, you'll also set your business on a path to minimize interruptions and avoid spammers, phishing scams and theft of your intellectual property by greatly enhancing the security of your email communications.


 WordPress Social Sharing at the speed of light.
WordPress Social Sharing at the speed of light. The Number 1 Web performance plugin for WordPress.
The Number 1 Web performance plugin for WordPress.